10 Security Issues in Cloud Computing Benefits Essay; Cloud security, otherwise called cloud computing security, comprises a bunch of technologies, procedures, controls, and policies that cooperate to ensure cloud-based infrastructure, data, and systems. These safety efforts arrange to secure cloud data, protect customers’ privacy, and also support regulatory compliance just as setting verification rules for singular devices and users.
Here is the article to explain, 10 Security Issues in Cloud Computing Benefits Essay!
Cloud computing offers three different segments to consumers – Infrastructure, Platform, and Application /Service as a service. Each of them provides different operations and services corresponding to business and individual. You may like to know, Bitcoin Use Cases Technology Essay; There are various concerns regarding security in a Cloud computing environment; also Servers & Applications accessibility, Data Transmission, VM Security, Network Security, Data Security, Data Privacy, Data Integrity, Data Location, Data Availability, Data Segregation.
The following 10 Security Issues in Cloud Computing below are;
Servers & Applications accessibility;
In Conventional data centers, the admin uses to access the servers in a restricted or controlled way through direct or on-premise connections. In Cloud architecture, the admin can access the system only through the internet which increases the risk and exposure of connection. While accessing the data by user, data access issues are primarily associated with security policies provided to users. To avoid unauthorized data access, that case, security policies should adhere to the cloud.
Data Transmission;
The data exists always transmitted from one end to another end in encrypted formatted. Also, SSL/TLS data transmission protocol is used here. By providing different access controls to Cloud providers for data transmission like authentication authorization, auditing for using resources, and by ensuring the availability of the Internet-facing resources at the cloud provider. To interrupt and change the communication, an intruder can place themselves in between the communication to the user; also, this type of cryptographic attack stands called ‘Man-in-the-middle’.
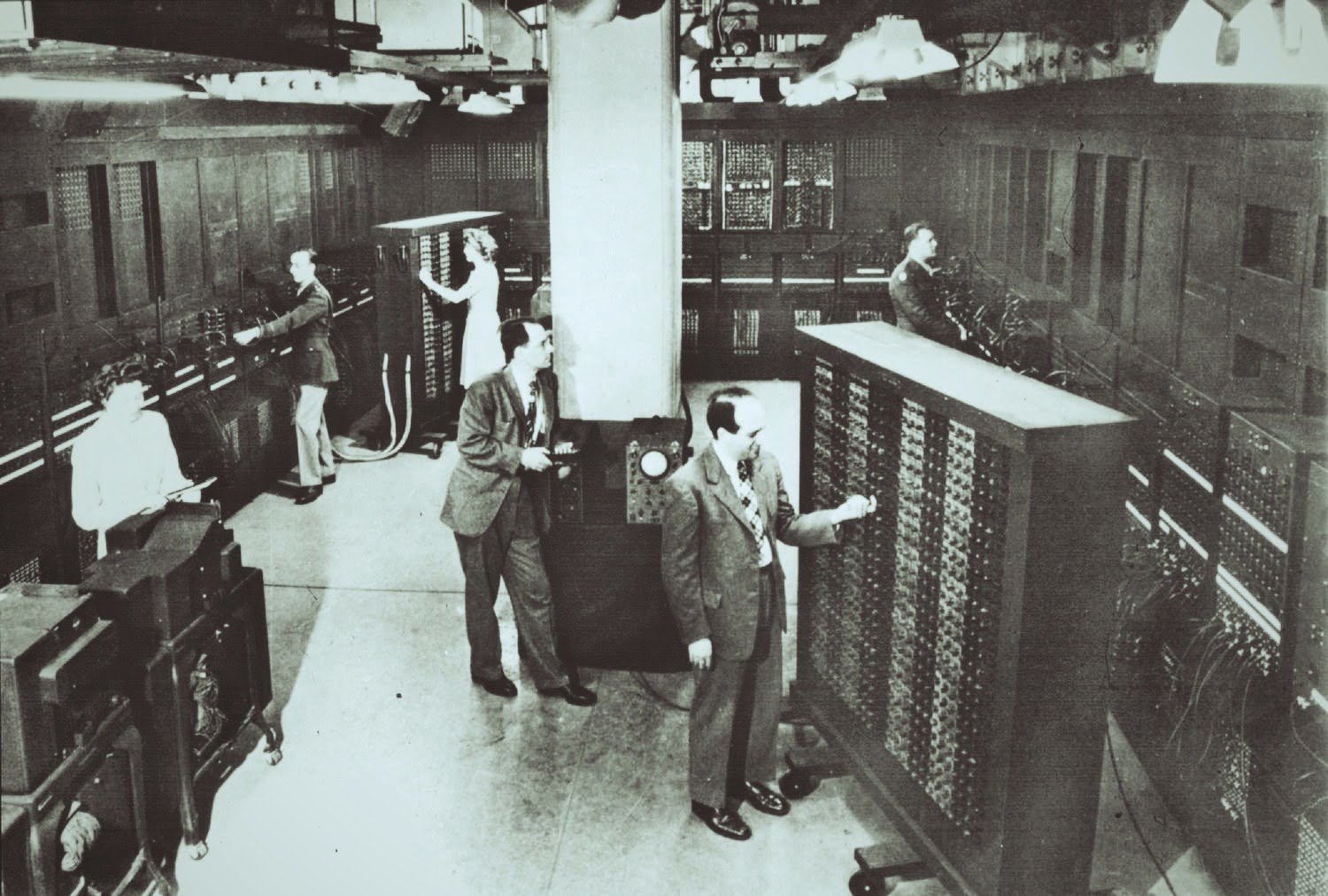
Virtual Machine Security;
Virtual machines are dynamic seamlessly moved between physical servers. Virtualization is one of the components of the Cloud which runs various isolated instances on the same physical machine is one of the allocated tasks of Virtualisation. Virtual servers like Microsoft are vulnerable to allowing a guest operating system to execute code on the host OS and other guest OS. The main loophole found in VMware’s shared folder terminology permits the guest systems to read and write in system files. Appropriate isolation methodology not implemented in current Virtual Machine Monitor (VMM). VMM should provide a secure environment so that none of the virtualized guests can access the host system.
Network Security;
The networks categorize into different types like public, private, shared, non-shared, and large or small areas. The network level is consists of these security problems like Sniffer attacks, DNS attacks, etc. In DNS attacks, a user can easily route to another Cloud server instead of what the user requested. Domain Name Security Extension (DNSSEC) lessens the number of DNS threats; but, it is not adequate to stop the re-routing of the connection to other servers.
Data Security;
Whenever users want to store their data on the Cloud, the Cloud providers use the most common communication protocol; which is Hypertext Transfer Protocol (HTTP). For ensuring data security and integrity, usage of Hypertext Transfer Protocol Secure (HTTPS) and Secure Shell (SSH) is common. In Cloud systems, the organization data saves out of premises. Cloud providers can use encryption techniques to avoid breaches. For instance, The Administrators of Amazon Elastic Cloud Computing (EC2) can’t access the user’s instances and do not have access to Guest OS. Administrators require their Cryptographically Strong Secure (SSH) keys to access the host instance. All accesses should log and audited timely.
Data Privacy;
With Data Security, Data Privacy is one of the primary concerns for Cloud service providers. Cloud providers should ensure the customer’s data privacy demand. Data on the cloud exists almost distributed globally; which increases the concerns regarding data exposure and jurisdiction. Cloud providers might be at risk of not complying with the policies of the government.
Data Integrity;
It helps to reduce the level of data corruption that occurs at storage. For data centers, integrity monitoring is crucial for Cloud storage. Database constraints and transactions contribute to maintaining Data integrity. For Data integrity, transactions should follow the properties of ACID (Atomicity, Consistency, Isolation, and Durability).
Data Location;
In Cloud data storage, users are not aware of the fact in which location the data is stored or accessed. To serve this purpose, Many well-renowned Cloud providers have data centers globally. Due to various countries’ data privacy laws and compliance, this could be an issue. In many enterprises, the location of data is highly prioritized. For example, Countries like South America have local laws and jurisdiction on a particular amount of sensitive information.
Data Availability;
The enterprises should ensure the availability of data round the clock without any hindrances. Due to the unpredictability of system failure, data providers are unable to attain that standard sometimes. To achieve the high scalability and availability of the system, service providers can make some changes at the application and infrastructure levels. A multi-tier architecture is the best option to achieve data availability seamlessly through load balancing and also running the instance on separate servers. For any emergencies, cloud providers should design an action plan to cope up with disaster recovery and to achieve business continuity.
Data Segregation;
In cloud architecture, data is typically shared among other customer data. To solve the data segregation issue, encryption is not the only solution to look at. In some cases, consumers don’t want to encrypt their data because it might destroy the data. Cloud providers should ensure that encryption provides at all levels; and also encryption should implement under the supervision of experienced professionals.
Benefits of Cloud Computing Security;
Cloud computing has created a tremendous boom in the recent technologies that help the business to run online, save time, and be cost-effective. Therefore, besides having a lot of advantages of cloud computing systems, cloud computing security also plays a major role in this technology that ensures clients use it without any risk or tension.
Below are the advantages or benefits of cloud security:
Security against DDoS attacks:
Many companies face the Distributed Denial of Service (DDoS) attack that a major threat that hampers company data before reaching the desired user. That is why cloud computing security plays a major role in data protection because it filters data in the cloud server before reaching cloud applications by erasing the threat of data hack.
Data security and data virtue:
Cloud servers are real and easy targets of falling into the trap of data breaches. Without proper care, data will be hampered, and hackers will get the hands of it. Cloud security servers ensure the best quality security protocols that help in protecting sensitive information and also maintaining data integrity.
Flexible element:
Cloud computing security provides the best flexibility when data traffic is concerned. Therefore, during high traffic user gets the flexibility in a happening server crash. The user also gets scalability resulting in cost reduction when the high flow of traffic ends.
Availability and 24/7 help system:
Cloud servers are available and provide the best backup solution giving a constant 24/7 support system benefitting the users as well as clients.






Leave a Reply